In this series we examine ways to make APM authenticate against multiple Active Directory Domains. Part 1 discussed the use of a drop down menu on the APM login page. In Part 2 we use the user’s UPN to determine the correct domain for authentication.
Note: If you are following along through the series I recommend that you create a new APM Access Profile for Part 2 versus modifying the Access Policy from Part 1.
Home Realm Discovery / Where Are You From
Depending upon your experience with multi-domain and/or federated authentication the terms “Home Realm Discovery” and/or “Where are you From” may seem odd. The basic principal of this page during an authentication process is to determine the user’s authentication domain/source by asking a question or providing a list of accepted domains/sources. In our example we will ask for the user’s UPN and based upon their response APM will choose the corresponding Active Directory domain for authentication.
For those that like to see the big picture first the image below provides an overview of the completed Visual Policy Editor for our Access Profile.

So lets get started…
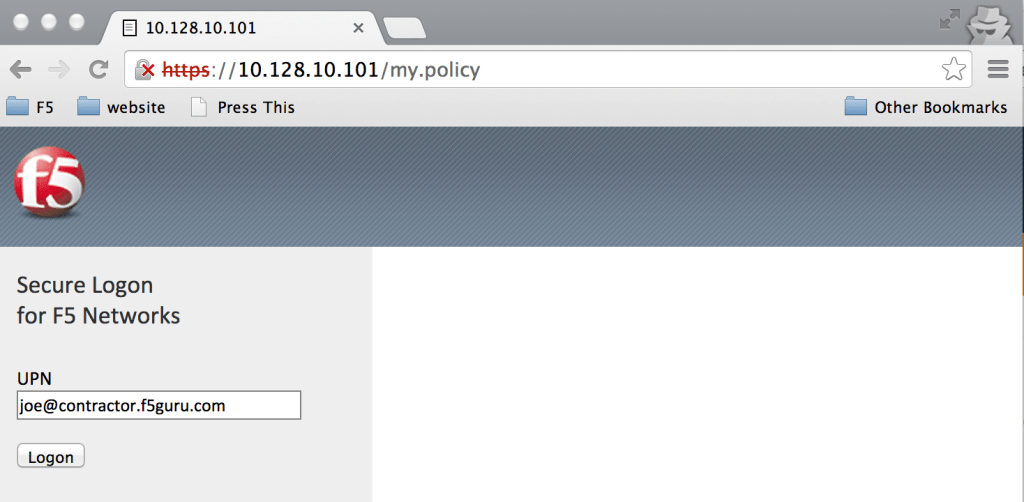
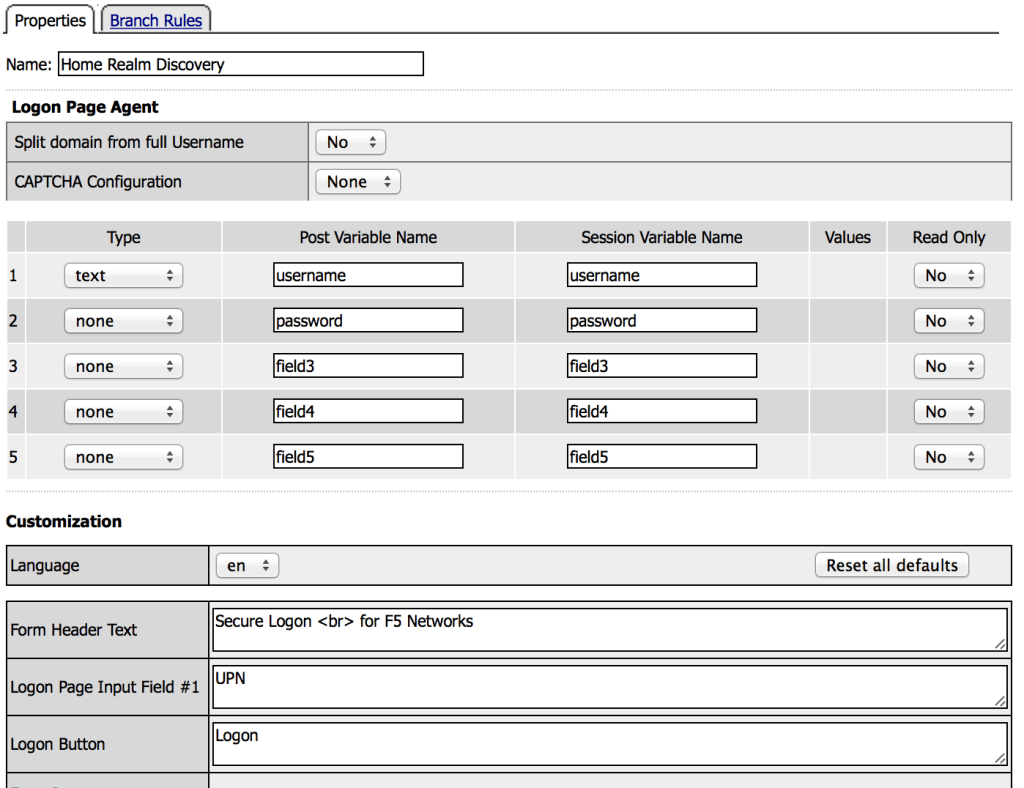
Home Realm Discovery Logon Page
In an empty VPE add a Logon Page action between the Start and Deny ending (click the (+) button if you’ve never edited the VPE before). Next you will need to make the following modification and then click Save.
- Change the type for Logon Page Input Field #2 to:
- None
- Change the text for Logon Page Input Field #1 to:
- UPN
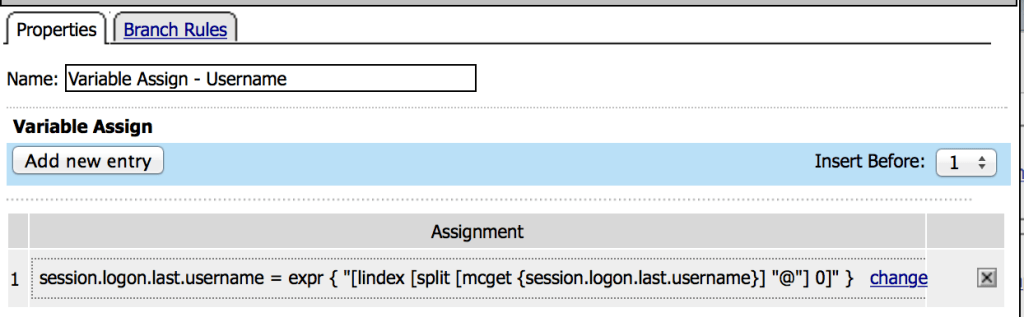
Convert UPN to Username
Since APM’s AD auth action by default authenticates users by username and not the UPN we’ll need to extract the username from the UPN. For this step you’ll need to add a Variable Assign action after the Home Realm Discovery Logon Page. Make the following modifications and then click Save.
- In the Custom Variable text box enter:
- session.logon.last.username
- In the Custom Expression text box enter:
- expr { “[lindex [split [mcget {session.logon.last.username}] “@”] 0]” }
Determine Authentication Domain
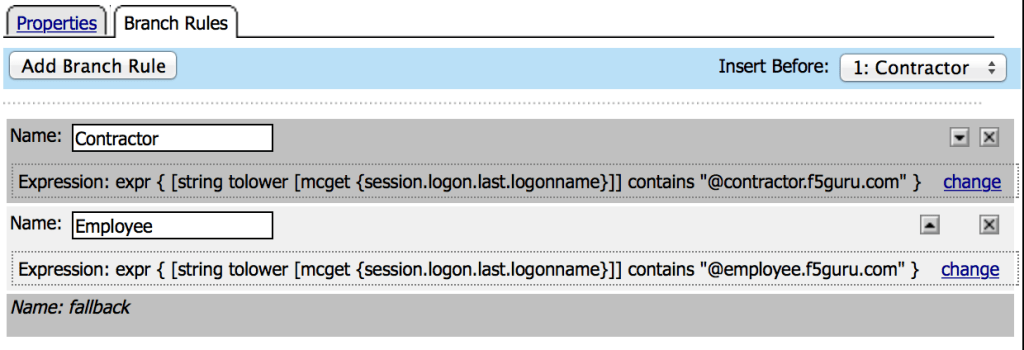
Next we’ll need to examine the UPN and determine which domain to user for authentication. For this step you’ll need to add an Empty action and create two Branch Rules (2nd tab at the top of the action window). Once you’ve configured your Branch Rules click Save.
Note: It is important that if you are copying/pasting the expressions that you remove any newlines that may result from browser formatting.
- Change the 1st Branch Rule’s Name to:
- Contractor
- Enter the following expression: (click change and then select the Advanced tab)
- expr { [string tolower [mcget {session.logon.last.logonname}]] contains “@contractor.f5guru.com” }
- Change the 2nd Branch Rule’s Name to:
- Employee
- Enter the following expression:
- expr { [string tolower [mcget {session.logon.last.logonname}]] contains “@employee.f5guru.com” }
Notice we’re examining the logonname and not the username. This is because the username was previously changed. The logonname is set by the Home Realm Discovery Logon Page and offers us a pristine copy of the UPN.
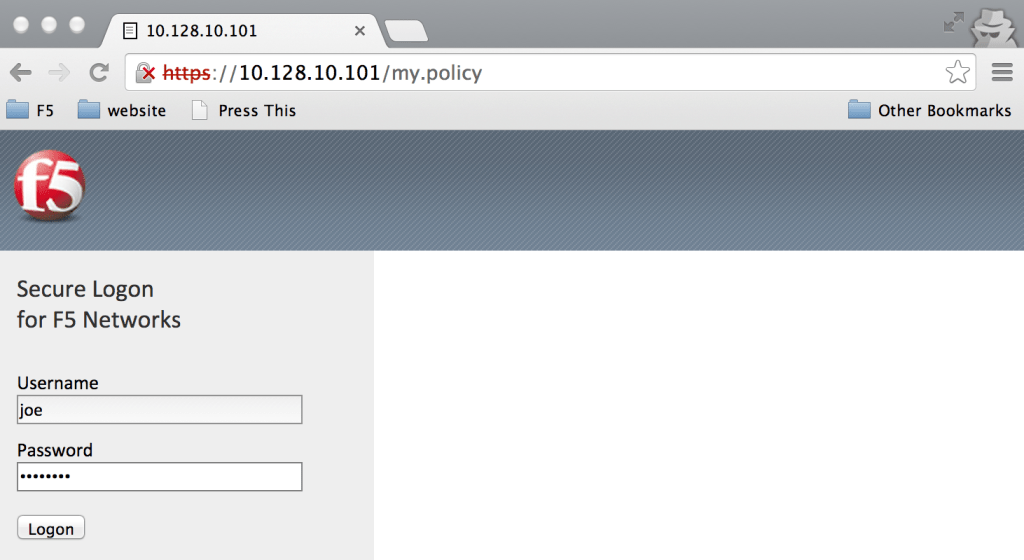
Domain Specific Logon Pages
Next we’ll need to create domain specific logon pages to request credentials. For each branch, contractor and employee, you’l need to add a Logon Page action and customize each logon page with the below settings and then click Save.
- Set the Read Only option to Yes for Logon Page Input Field #1
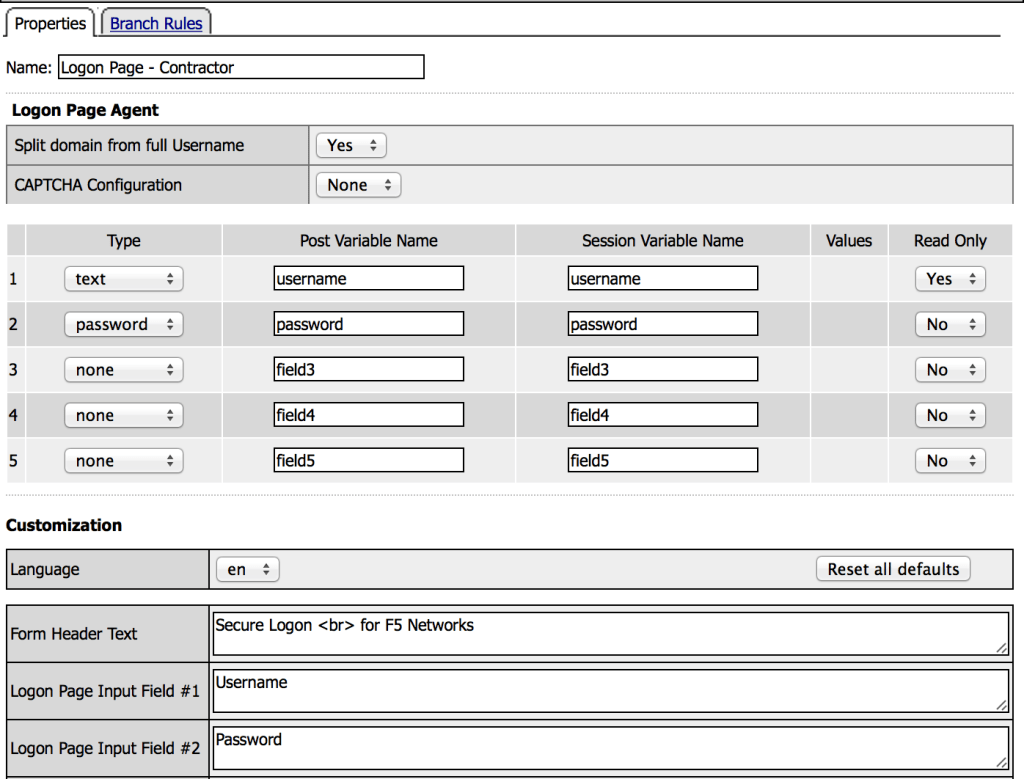
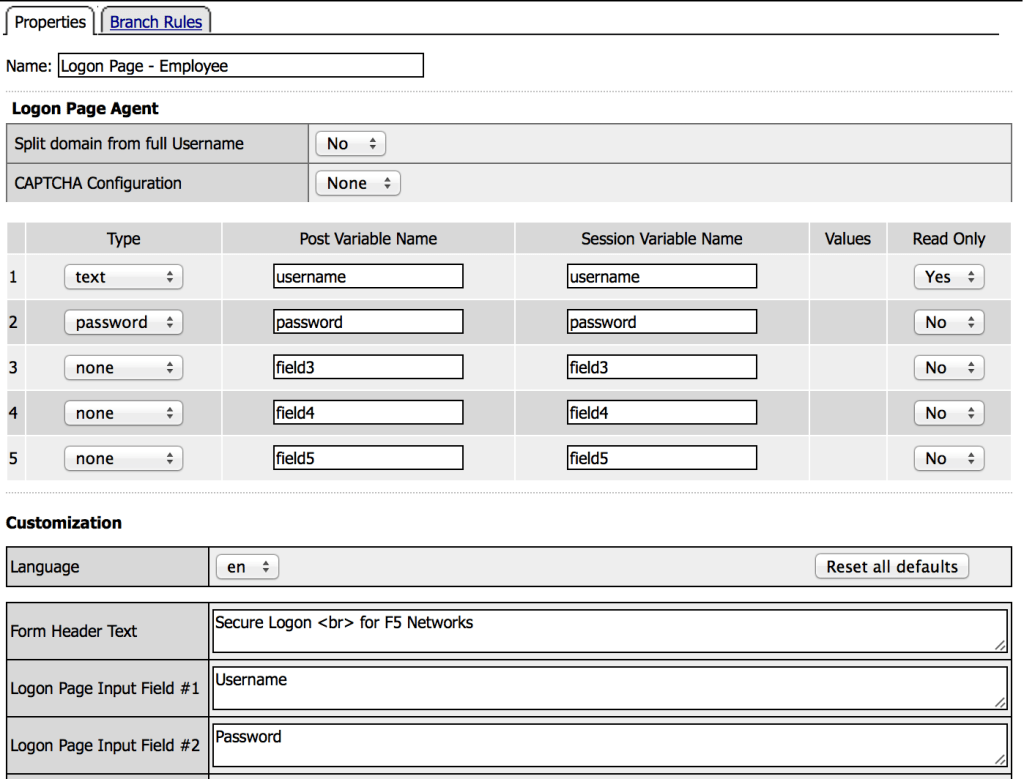
In this example I am only asking for the user’s password but this demo could easily be modified to require multi-factor authentication and/or send the user to RSA for risk based authentication.
Domain Authentication
From here, you can add an AD Auth action to each branch, contractor and employee, and configure the Server to the corresponding AAA object for the selected domain.
End Results
The final results will prompt the user for their UPN, then their password and authenticate the user against the desired domain. In the next post we’ll look at ways to obtain the correct domain by querying the Active Directory Global Catalog or specific domain.